Research Project
Description
Trident is a lightweight framework to train and test cyber agents (benign, attacker, defender) in real-like environments using Docker and standard DevOps toolchains. The project is motivated by the need to evaluate defensive tactics, automate detection and response, and stress-test agents against realistic attack patterns while keeping experiments reproducible and containerized.
Main Goal
Build and validate defender agents that operate reliably in containerized real-world stacks, while supporting benign and attacker agents for realistic training and evaluation.
Collaboration
Developed in collaboration with Stratosphere Laboratory at CTU UNIVERSITY, PRAGUE, leveraging years of expertise in network security and intrusion detection systems.
Workflow Phases
Infrastructure & Integration
Establishing a closed-loop system where an attacker triggers alerts, prompting the defender to act.
Realism & Calibration
Injecting benign user traffic to measure false positives and refine detection logic.
LLM Red Teaming
Conducting manual and automated red-teaming to test the defender against prompt injections.
Expansion
Scaling to complex network topologies to test advanced detection models (Temporal GNNs).
Technical Components
Trident enables agents to execute unrestricted code in isolated Docker containers, generating real network traffic, alerts, and defensive actions.
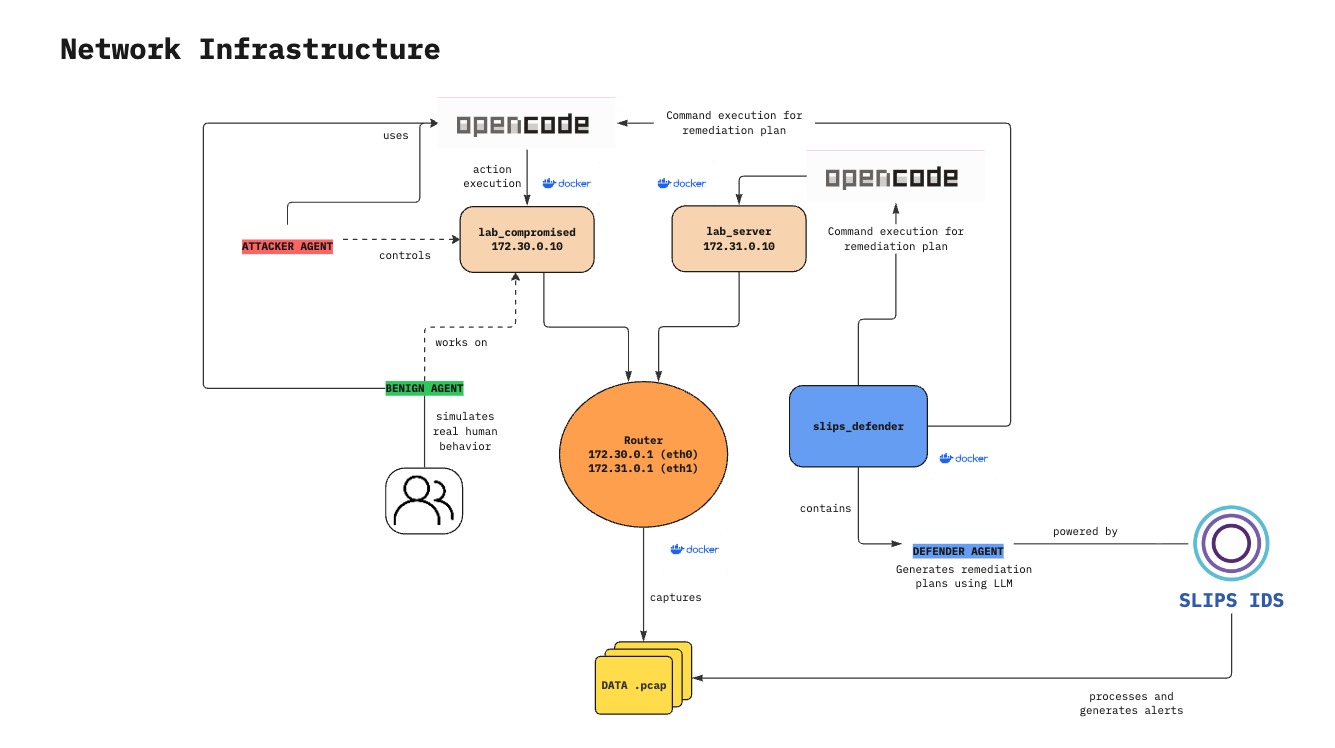
Defender Agent
Monitors alerts, generates defensive prompts, and executes responses via OpenCode on victim machines.
Attacker Agent (aracne)
Performs controlled attack scenarios from an external host to validate detection and response.
Benign Agent (Ghost)
Simulates realistic user behavior to test false positive rates and system noise.
SLIPS
Network intrusion detection system that generates alerts from observed traffic patterns.
Docker Infrastructure
Containerized victim machines and servers providing isolated, reproducible environments.
Alert Pipeline
Forwards SLIPS alerts to the defender via FastAPI service for real-time response.
Research Impact
The impact and capabilities Trident will enable for the cybersecurity research community.
Trustworthy Evaluation
A safe, isolated sandbox for benchmarking unrestricted command execution by benign, attacker, and defender agents on real systems.
Reproducible Environment
An environment that mirrors real networks, supports larger topologies, and allows safe experimentation without risk to production systems.
Defensive Automation
Improved agent reliability through high-quality prompts, structured execution paths, and consistent response policies validated by testing.
Reduced False Positives
Better understanding of operational noise through calibrated benign activity that resembles real user behavior.
High-Quality Datasets
Rich network and host-level datasets enriched with MITRE ATT&CK tags, supporting offline analysis and ML experimentation.
Extensible Framework
A modular platform where new sensors, autonomous agents, or detection components are pluggable without redesigning the environment.
Open Source Tools
GitHub Repositories
- SLIPS - Network Intrusion Detection System
- NetSecGame - Network Security Game Framework
- aracne - Attacker Agent
- Trident - Main Repository
Related Tools
- StratoCyberLab - Cyber Range Platform
- GHOSTS - Benign Activity Generator
Research Partnership
Trident is developed by a research team from Mendoza, Argentina, part of LABSIN (Laboratory of Intelligent Systems) at Universidad Nacional de Cuyo. We work in close collaboration with Stratosphere Laboratory at CTU UNIVERSITY, PRAGUE and Strato on various cybersecurity projects and autonomous agent development.
Project Roles
- Project coordinator & senior AI expert
- Main developer
- Junior developer & Docker specialist